Everything visible.
No commands to memorize.
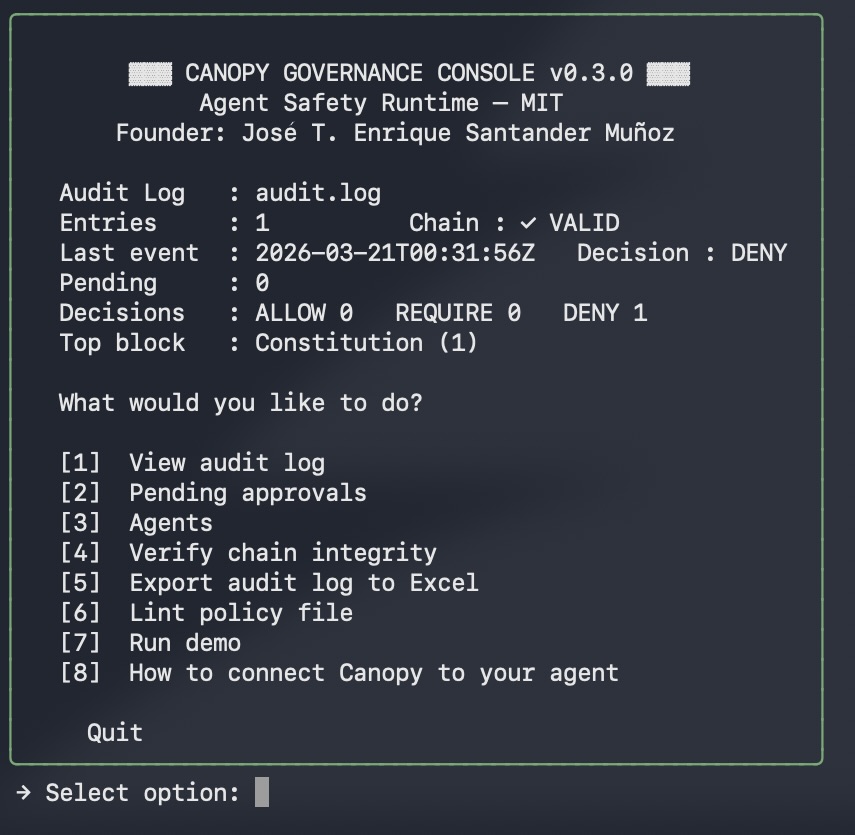
One command. Every governance tool in one screen. Built for teams that need operational visibility without friction.
Canopy decides whether an agent action should be attempted - before execution. Deterministic. Auditable. Wired in under one hour.
The agent received a valid instruction. Built a real command. The filter was wrong - staging values, production instances. No gate. No log. No answer for the postmortem.
# Agent: "clean up old staging resources" # Scope error. Nobody checked. aws ec2 terminate-instances \ --instance-ids $(aws ec2 describe-instances \ --filters Name=tag:env,Values=staging \ --query 'Reservations[].Instances[] .InstanceId' \ --output text) ✗ Production instances terminated. No gate. No log. Who approved this? Nobody knows.
from canopy import authorize_action result = authorize_action( agent_ctx={ "public_key": "pk-devops-agent-001", "created_at": "2026-01-01T00:00:00Z", }, action_type="execute_shell", action_payload={"command": dangerous_cmd}, ) Decision : DENY [critical] Reason : denied before execution Audit ID : 9c2f3a8b... This entry exists before AWS was called.
Every action passes through four layers in sequence. The first non-ALLOW decision short-circuits the pipeline.
The layers field in every response shows exactly
what fired and what was skipped.
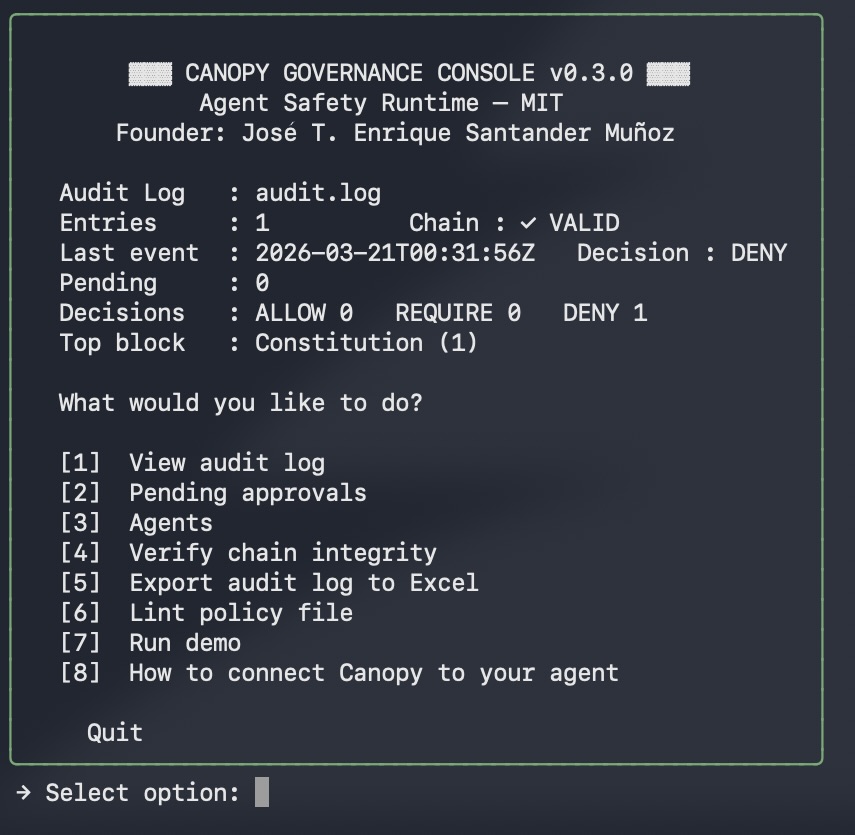
One command. Every governance tool in one screen. Built for teams that need operational visibility without friction.
When an AI agent causes an incident today, nobody can answer these with technical evidence. Canopy produces a signed audit entry for every action - before it runs.
terminate-instances call?"Every decision writes a tamper-evident, hash-chained entry before any command runs. Verifiable. Exportable. Ready for incident review.
Every entry chains to the previous via SHA-256. Modify any past entry and verification breaks from that point forward.
canopy-verify audit.logThe audit entry is written before the command runs. The authorization_id links authorization to the execution path that followed.
One command produces a formatted spreadsheet with color-coded decisions and a summary tab, ready for management and incident review.
canopy-report audit.log --export audit_report.xlsxThe pre-execution governance layer that was missing from your stack. One Python call. One log file. Zero new infrastructure. Wired in under one hour.